Fraud losses are estimated to reach $41.06 billion by 2030, tied to total card volume of $70.731 trillion. This data highlights that the security of credit card transactions is ever at issue, and increasingly so. Non-compliance with PCI DSS can result in fines ranging from $5,000 to $100,000 per month, increased audit requirements, and potential lawsuits.
As the processing of credit card payments always involves several parties, it is essential for the credit card industry to adopt an end-to-end approach to eliminate potential vulnerabilities and security gaps. One of the main tools in achieving this goal is the Payment Card Industry Data Security Standard (PCI DSS). This set of requirements came into being back in 2004 as an initiative by 5 major credit card issuers (Visa, Mastercard, American Express, JSB, and Discover) and has since become a prevailing compliance standard for all businesses involved in credit card transactions worldwide. Non-compliance also increases the risk of data loss, which can severely impact business operations, consumer data protection, and security posture, especially for companies that store credit card data.
We’ll examine the compliance levels PCI defines, as well as some of the differences in the ways the different card issuers interpret them. Our goal is to help you establish a compliant and robust process of handling payment card data in accordance with the vendor-specific requirements relevant to your case.
Key Takeaways
- There are four PCI DSS compliance levels for merchants and two for service providers, each with different validation requirements.
- Compliance levels scale with risk: the more transactions you process, the stricter the controls and validation requirements.
- Your PCI level determines whether you need an external audit, annual report, or just a self-assessment questionnaire (SAQ).
- Quarterly network scans and ongoing vulnerability management program activities are required across most compliance levels.
- Misclassifying your PCI level can lead to failed audits, penalties, or increased exposure to data breaches.
What Is the PCI DSS Standard?
In essence, PCI DSS is a set of policies and related procedures designed to achieve one major goal: to maximize the security of card transactions throughout their lifecycle by preventing malicious actors from using credit card data. Notably, it deals not only with credit card transactions, but also with those involving debit cards and cash cards.
The PCI requirements describe how such cards are to be processed securely, i.e., how organizations process cardholder data, including how it is collected, transmitted, and stored within the cardholder data environment. Besides, they detail the best practices that are to be employed to accomplish this objective. The standard includes 12 objectives and 281 guidelines that organizations must follow to meet compliance requirements before accepting payments.
Need deeper insights into the ways to ensure data security in fintech applications? Find the best practices from our developers in a dedicated article.
Despite being widely accepted, PCI DSS is not a legal requirement in any of the geographies where it is used. Simultaneously, the virtually universal use of PCI and its inclusion in legal agreements by the vast majority of credit card market players makes it rather unavoidable for card-processing businesses to comply with the PCI requirements.
To outline and help create a secure card-processing environment, PCI DSS defines:
- 6 main principles around which PCI DSS compliance is centered.
- 12 requirements business organizations need to meet to ensure the security of their card processing for systems that store cardholder data using point-to-point encryption.
- 4 levels of PCI DSS compliance for merchants, defined and applied in accordance with the yearly number of transactions a business handles.
- Self-assessment guidelines that merchants and service providers can use to self-evaluate the level of their compliance with the PCI DSS requirements.
- The best practices that help achieve PCI DSS compliance.
The latest version, PCI DSS 4.0, was published in March 2022, marking a significant update to the standard. The PCI DSS 4.0 requirements are organized into six categories, which help address different aspects of data security and provide a structured framework for organizations to follow, including physical access safeguards.
PCI compliance levels are primarily determined by annual transaction volume. However, validation requirements and thresholds may vary slightly depending on the payment card brand (e.g., Visa, Mastercard, American Express).
Each level defines not only the volume threshold but also the required validation approach, ranging from self-assessment questionnaires to full external audits conducted by qualified security assessors.
Although PCI norms are universal across all participating credit card brands, each brand has a separate PCI DSS compliance enforcement program. The latter accounts for some differences in the ways they interpret the merchant compliance levels and related compliance requirements.
Make sure your business meets the important requirements with our PCI DSS compliance checklist.
Let’s now look at the merchant compliance levels and the procedures that merchants need to undergo to provide compliance with each of these levels.
Level 3
Level 3 of PCI DSS merchant compliance is associated with businesses that process from 20,000 to 1 million transactions per year. The transaction volume of American Express for this level is from 10,000 to 50,000 American Express Card transactions. With American Express, the level applies only to merchants. For Mastercard, in turn, the set transaction volume is for a combined total of Mastercard and eCommerce Maestro transactions.
To achieve this level of compliance, merchants must:
- Complete and submit an annual self-assessment questionnaire.
- Submit an attestation of compliance form that states the company has fulfilled all the corresponding compliance requirements.
- Undergo quarterly network scans of the company’s network by an approved scanning vendor.
For Mastercard, only a SAQ is required. Unlike with Levels 1 and 2, Level 3 and Level 4 of PCI DSS compliance stipulate no requirement for mandatory penetration testing. Please note, that mandatory according to PCI DSS 4.0, penetration testing should not be mixed up with vulnerability network scans.

Andrii Semitkin
Delivery Director at SPD Technology
“PCI compliance is not a mere formality, it’s a tool called to prevent unwanted scenarios. In this sense, penetration testing is an awesome approach that allows you to unearth real vulnerabilities, check whether the safeguards you have in place protect you 24/7 without any dodgy downtimes, and gauge how well these safeguards can actually respond to various threats.”
Level 4
Level 4 of PCI merchant level compliance is for merchants that process less than 20,000 transactions per year. The transaction volume of American Express for PCI compliance level 4 is less than 10,000 American Express Card transactions. With American Express, the level applies only to merchants. For Mastercard, this level applies to merchants other than those that fall under the other 3 levels. Level 4 typically applies to small businesses, and the compliance process is generally easier to validate than at higher levels.
To achieve this level of compliance, merchants must:
- Complete and submit a self-assessment questionnaire, or comply with some alternative validation requirements set by the acquiring bank.
- Undergo a vulnerability scan of the company’s network by an authorized scanning vendor on a quarterly basis.
- Submit an attestation of compliance form that states the company has fulfilled all the corresponding compliance requirements.
Notably, compliance with Level 4 of PCI also requires that the company has not fallen victim to a successful cyber attack or suffered data breaches.
Please note, that the application of some of the different PCI DSS merchant compliance levels may differ for those companies that have not suffered a data breach or successful cyber attack and those that have. For example, the former may be subjected to Level 1 compliance even if their volume of transactions is lower than that envisaged by this compliance level.
In the case of Level 2 compliance, a business that has suffered a data breach or successful cyber attack may be requested to undergo an on-site PCI audit or compose and submit an annual report.
A Self-Assessment Questionnaire (SAQ) & How to Deal with It
As we can see from the sets of procedures to be completed for the different PCI DSS levels, self-assessment questionnaires are an integral part of the PCI compliance that merchants handle on their own. Because of this, we’d like to say a few words about how exactly they should approach this part of PCI compliance.
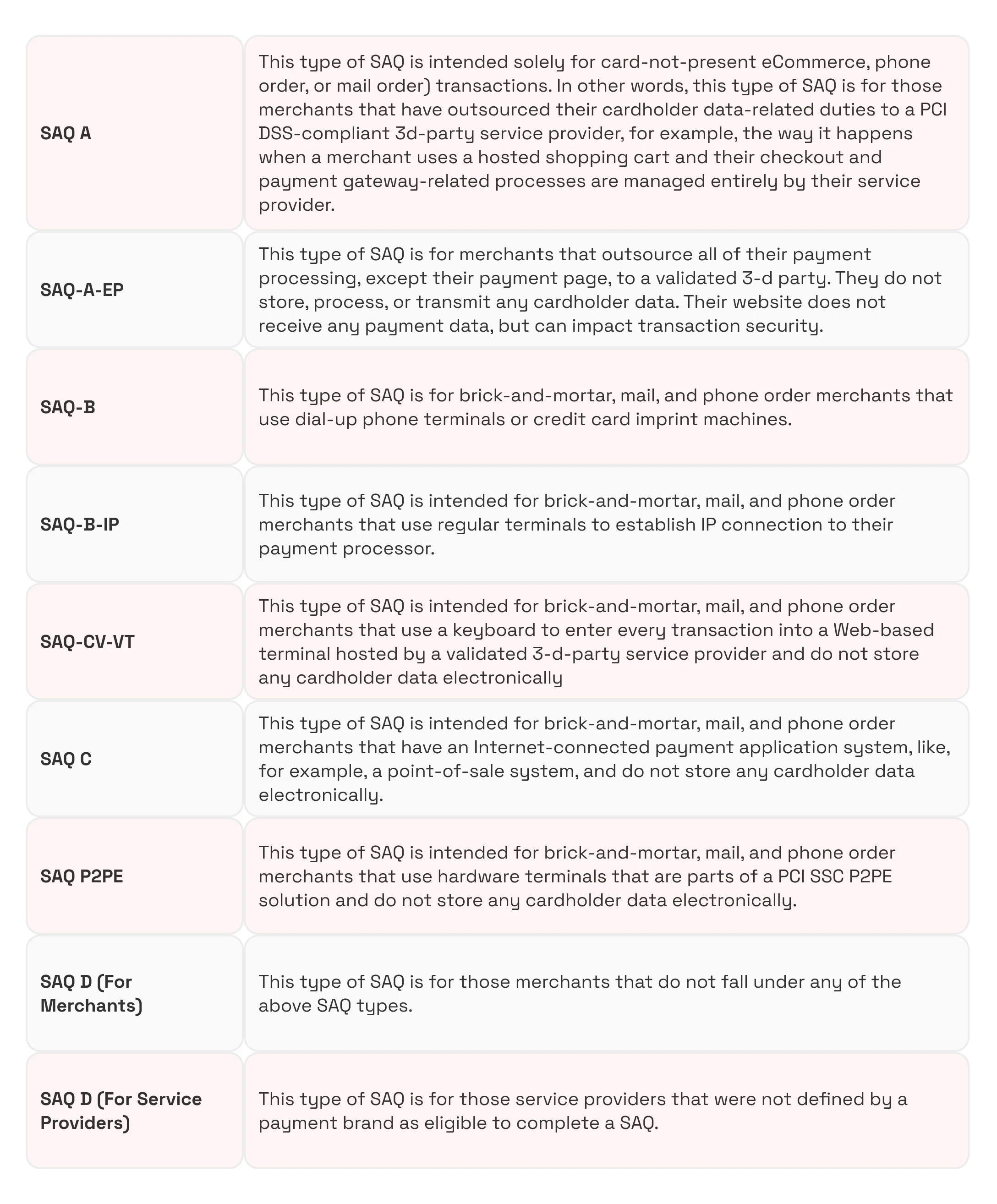
So far, the Payment Card Industry Security Standards Council has introduced 9 types of SAQ. The types of devices and systems used for card-not-present transactions determine which SAQ applies to a merchant. Each of these SAQ types comprises 12 sections, each devoted to one of the 12 PCI DSS requirements. In turn, each of these 12 sections contains 6 control objectives.
The self-assessment questionnaire consists of a series of yes-or-no questions for each applicable PCI compliance requirement. The SAQ is designed to ensure the security of payment card and account data across all relevant systems and devices involved in payment processing. The expected testing column of an SAQ describes the testing activities used to establish whether a merchant is PCI-compliant with the corresponding requirement.The types of SAQs are as follows.
How to Approach a Self-Assessment Questionnaire
To begin the SAQ completion process, merchants first need to select the SAQ type that is appropriate to the nature of their business, for example, SAQ A or SAQ C. Next, they need to obtain the required forms from the PCI Security Standards Council website.
As the next step, it makes sense to first get familiar with the requirements your SAQ contains and collect or additionally obtain any relevant evidence of compliance with these requirements. Such evidence can be diverse: security policies, descriptions of the implemented security procedures, network diagrams, penetration test results, and any other relevant document assets.
After this, one should answer the questions the SAQ contains in good faith. In answering the questions, one should provide a description of any relevant compensating controls that they have in place. Lasly, one should identify those areas where your business falls short of the PCI requirements and come up with measures to stop any existing gaps.
VISA and Mastercard PCI DSS Compliance Levels for Service Providers
The PCI compliance validation levels for service providers (or any organization that processes, transmits, and stores card-related information, usually on behalf of an acquiring bank, merchant, or another payment service provider entity) differ from those for merchants. Service providers are classified into two levels based on transaction volume, and this two-tier system is stricter because service providers often handle data for multiple clients on behalf of an acquiring bank. For example, the following apply to Visa.
Level 1
Level 1 of PCI DSS service provider compliance is associated with VISA.Net Processors or any other service providers that store, process, and/or transmit more than 300000 transactions per year. These service providers must:
- Submit an annual report of compliance done by the QSA.
- Undergo quarterly network scans by an ASV.
- Submit an attestation of compliance form.
Level 2
Level 2 of PCI service provider compliance is associated with any service providers that store, process, and/or transmit less than 300,000 transactions per year. The service providers must:
- Undergo a quarterly vulnerability network scan by an ASV.
- Submit an attestation of compliance form.
Similarly, Mastercard has 2 PCI compliance service provider levels with the same transaction volumes and provides a detailed listing of the types of service providers that fall under each of these levels.
PCI DSS Readiness Checklist for Fintech Product Companies
Use this checklist to evaluate your preparedness as part of PCI DSS readiness strategies for fintech. It covers the main technical and operational areas that typically impact compliance outcomes for fintech products.
- Align compliance with product architecture. Ensure PCI DSS requirements are considered when designing systems, not added later.
- Validate your PCI compliance level early. Use a compliance checklist before accepting payments, as incorrect classification can lead to audit issues and unexpected requirements.
- Design secure data handling flows. Structure how customer data moves through your product to minimize risk points.
- Decide on build vs. outsource for payments. Using PCI-compliant providers can significantly reduce your compliance burden.
- Control access to sensitive systems. Limit who can interact with payment data and track all access activities using strong access control measures.
- Integrate security into development workflows. Make security checks part of releases, not a separate phase.
- Ensure infrastructure supports scaling securely. Plan for growth without breaking compliance requirements.
- Prepare for audits or self-assessment. Know whether you need an external qualified security assessor audit or can rely on SAQ validation.
- Monitor compliance continuously. Treat PCI as an ongoing process, not a one-time milestone.
- Train teams on compliance responsibilities. Make sure engineering and product teams understand how their decisions impact PCI scope.
Conclusion
Understanding the PCI DSS levels is instrumental in achieving PCI DSS compliance and ensuring cardholder data security in Fintech, particularly for various card-processing businesses.
However, it’s also important to realize that PCI compliance is both a practical boon and a technical challenge that one must meet with sufficient efficiency. In fact, it may involve dealing with several Fintech development challenges that take quite a bit of skill to solve.
If you want to learn more about some technical aspects of achieving PCI compliance or PCI DSS audit, you are always welcome to get in touch with our compliance software development experts.
Disclaimer! The merchant and service provider-related PCI DSS compliance information herein is provided for the purpose of gaining an overall understanding only and does not represent an exhaustive, accurate, or comprehensive analysis of the matter. You must become thoroughly familiar with the corresponding original PCI DSS requirements and card brand-related specifics prior to handling any PCI DSS compliance-related matters.