As we continue to discuss the realm of Fintech and building custom software solutions for this industry, it’s time to cover one of the most prominent aspects of any financial software, ensuring Fintech data security.
In our previous articles, we discussed how to build a payment gateway and how much it costs. This time, we will focus on PCI DSS compliance requirements, the most important aspect of information security and data protection for any company processing financial information online.
What makes data security and PCI DSS compliance one of the most crucial considerations for fintech companies? According to IBM, the global average cost of a data breach in 2025 was USD 4.4 million. In addition to that, your business may be penalized by up to $100,000 a month for being non-compliant with PCI DSS, so this is critical for organizations dealing with financial transactions.
PCI DSS requirements were designed to better control cardholder data and reduce credit card fraud. The latest version was made available in March 2022 by the PCI Security Standards Council. Its changes are significant and introduce additional potential security vulnerabilities and risks compared to previous versions.
Key Takeaways
- Secure architecture (not just tools) is the foundation of protecting cardholder and customer data.
- PCI DSS compliance directly impacts customer trust, partnerships, and your ability to operate in global markets.
- Most data breaches stem from poor access controls, weak passwords, and a lack of monitoring — not advanced attacks.
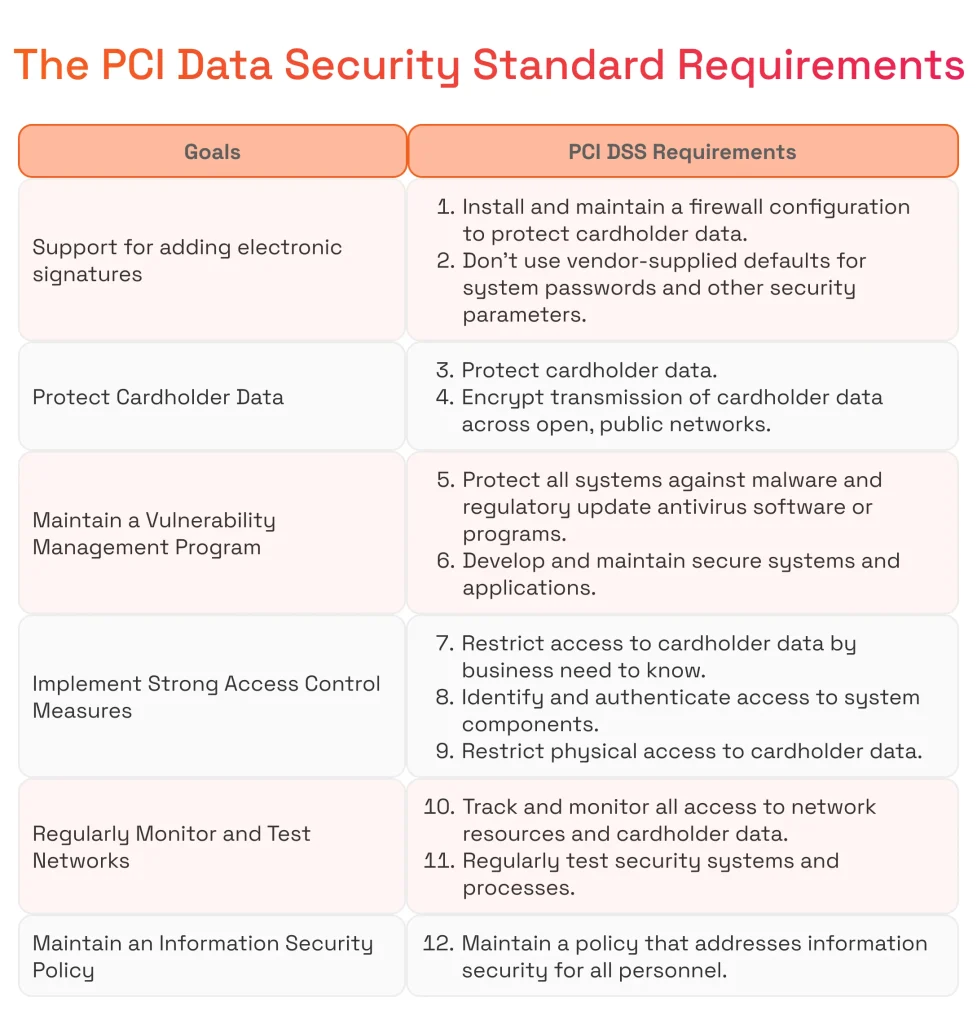
- There are 12 PCI requirements that every organization handling cardholder data must follow. These requirements are grouped under 6 control objectives that cover various aspects of security.
- Compliance requires alignment between engineering, security, and business processes to improve your security posture.
- Treat PCI DSS as a business enabler, not just a regulatory burden.
Why Ensuring PCI DSS Compliance Is Important?
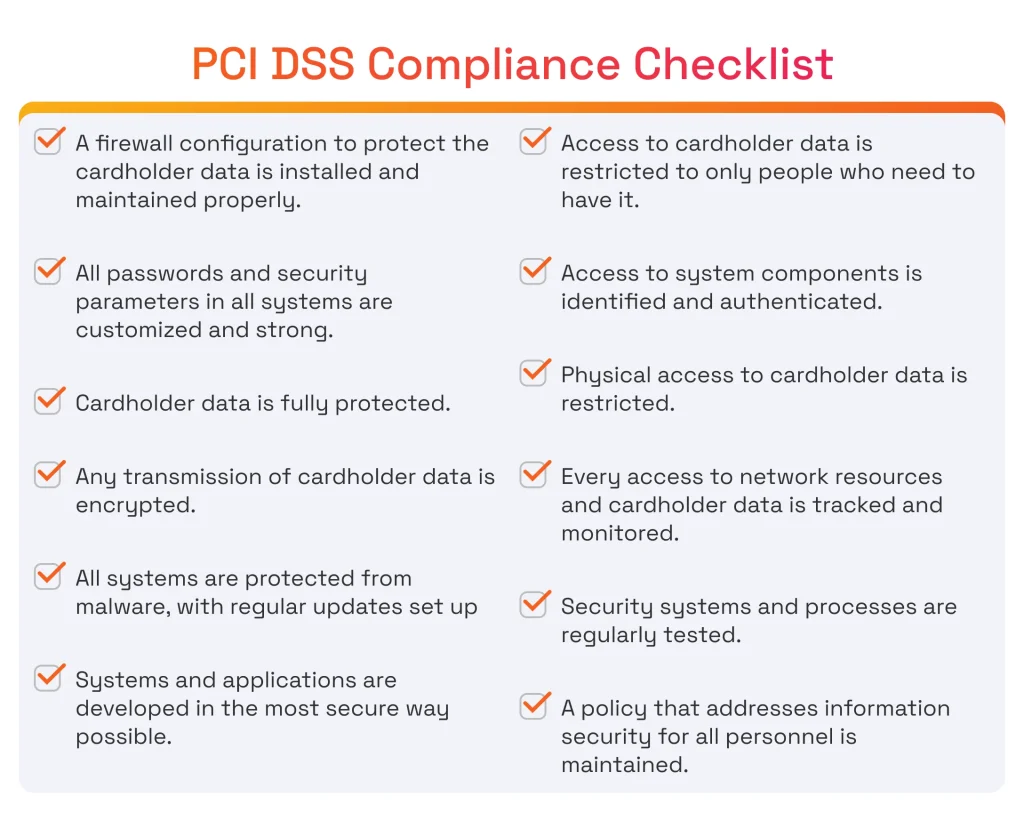
Following the PCI compliance checklist helps you safeguard cardholder data, maintain customer trust, prevent fraud, avoid financial losses, and implement continuous risk assessment. PCI compliance practices ensure the continuity of business operations.
Let’s discuss these points in more detail.
Protection of Cardholder Data
The main reason to follow the PCI DSS compliance requirements checklist in the first place, is that the standard is aimed at protecting cardholder data during its processing, transmission, and storage in your organization. It leverages such techniques as encryption and access controls, to help prevent unauthorized access and potential breaches of sensitive payment information.
Do you want to better understand how PCI DSS fits into broader regulatory requirements? Read our article on payment processing compliance and existing standards.
Customer Trust, Confidence, and Identity Theft Prevention
Your reputation matters since the brand image can make or break an organization. Adhering to PCI DSS, implementing KYC standards in financial services, and following other regulatory frameworks designed to enhance security, reduce fraud, and protect sensitive information. Full PCI compliance earns your organization an exceptional reputation. When your customer knows that all payment information and customer data are handled at the highest level of security, it builds trust in your company and becomes a great foundation for potential growth.
Following the PCS DSS checklist, or any other regulatory framework for that matter, does not guarantee 100% incident-free operation. However, it is safe to say that it dramatically reduces the risk of fraudulent activities and unauthorized transactions. Security measures such as strong access controls and regular monitoring help detect and prevent suspicious activity, resulting in a safer environment for your organization.
Avoidance of Data Breach Costs
PCI DSS encourages continuous monitoring and risk management practices, as regular assessments and monitoring help organizations stay vigilant against emerging threats and vulnerabilities through regular risk assessment. It allows for timely response and adaptation to changing circumstances.
Global Business Operations, Partnership, and Vendor Requirements
Many global businesses, payment processors, and major credit card companies require PCI DSS compliance as a prerequisite for partnerships and collaborations. So, PCI DSS compliance unlocks new opportunities for your business and helps you meet the expectations of partners, vendors, and regulatory bodies.
Efficient Incident Response and Business Continuity Preservation
The PCI DSS compliance audit checklist also includes a well-defined incident response plan, which ensures organizations are prepared to address and mitigate security incidents when they occur. This plan helps preserve business continuity and minimize potential downtime.
Demonstration of Due Diligence
Compliance efforts showcase a commitment to meeting standards, reducing risks, and helping protect customer data alongside payment card data.
Adaptability to Changing Threat Landscapes
The threat landscape is extremely dynamic, with new risks and vulnerabilities emerging regularly, requiring strong information security practices. PCI DSS compliance encourages organizations to stay adaptable and responsive to changing cybersecurity threats, fostering a proactive approach to security.
Now, let’s take a closer look at the PCI compliance checklist and discuss its most important aspects.
Not sure what PCI requirements apply to your business? Read our article on PCI DSS compliance levels for merchants and service providers.
Compliance Checklist Before Accepting Payments
#1. Define PCI DSS Scope and Cardholder Data Environment
This PCI compliance requirement focuses on identifying all systems, processes, and network components that interact with cardholder data. Properly defining the Cardholder Data Environment (CDE) is essential for limiting the PCI DSS scope and reducing compliance complexity.
Tips for compliance
- Clearly define what constitutes cardholder data, including primary account numbers (PAN), authentication data, and any sensitive data elements.
- Identify and document all systems that store, process, or transmit cardholder data across your infrastructure.
- Map data flows to understand how cardholder data moves between systems, applications, and external partners.
- Implement network segmentation to isolate the CDE from other network resources and reduce exposure.
- Regularly review and update the scope as systems and integrations evolve.
#2. Install and Maintain a Firewall Configuration
Firewall configuration is a foundational PCI DSS requirement that helps secure systems by enforcing strict control over network traffic. It defines how data flows across network boundaries and prevents unauthorized access to sensitive environments.
Tips for compliance
- Install firewalls at network perimeters and between different segments within the CDE to establish secure zones and control traffic between trusted and untrusted networks.
- Implement a default deny rule on firewalls to block all incoming and outgoing traffic, preventing attempts to gain unauthorized access.
- Implement network segmentation to isolate the CDE from other parts of the network.
- Use Access Control Lists (ACLs) to define and enforce network traffic policies, explicitly specifying which IP addresses, protocols, and ports are allowed or denied.
- Enable logging on firewalls and review firewall logs for suspicious activity or security incidents.
- Remove any unnecessary or outdated rules to reduce the attack surface.
- Document and review any changes to firewall rules to ensure they comply with the latest security policies and PCI DSS requirements.
- Consider inspecting and controlling traffic at the application layer.
- Conduct regular penetration testing to identify vulnerabilities and test network defenses within the firewall configuration.
#3. Remove Vendor-Supplied Defaults for System Passwords & Other Security Parameters
This can be a major problem in big organizations and systems with a high number of elements.
Tips for compliance
- Immediately change all default passwords and usernames on systems, devices, and applications upon installation.
- Ensure that all systems handling cardholder data are PCI DSS compliant and use strong passwords along with multi-factor authentication.
- Regularly update and rotate passwords.
- Scan systems using automated tools to detect default passwords and remediate any instances where default credentials may still be in use.
#4. Implement Network Segmentation and Secure Network Architecture
This requirement focuses on designing a secure network architecture that isolates sensitive systems and reduces the PCI DSS scope. Proper network segmentation helps prevent unauthorized access to the Cardholder Data Environment.
Tips for compliance
- Design network architecture with clearly defined trust boundaries.
- Isolate payment systems and cardholder data from general corporate networks.
- Implement layered controls across security systems, including firewalls, intrusion detection systems, and security protocols.
- Restrict communication between segments based on business need-to-know.
- Perform regular segmentation validation through penetration testing and audits.
Modern Card Platform Security Requirements
#5. Protect Stored Cardholder Data
The goal here is to secure sensitive information related to debit and credit card data to prevent unauthorized access and potential breaches.
Tips for compliance
- Clearly define and identify what constitutes cardholder data within your organization.
- Implement strict access controls to limit access to cardholder data on a need-to-know basis, ensuring that only authorized personnel can access sensitive information.
- Enable detailed logging and file integrity monitoring for all systems that handle stored cardholder data.
- Implement secure storage practices for physical and electronic cardholder data, including the protection of encryption keys.
#6. Encrypt Transmission of Cardholder Data Across Public Networks
Transferring data over networks, especially public networks, puts sensitive data at risk, so there is a need to enhance the security of cardholder information.
Tips for compliance
- Use strong encryption protocols such as TLS (preferably) or SSL to encrypt cardholder data during transmission. PCI DSS explicitly recommends discontinuing the use of early versions of SSL due to exposed vulnerabilities.
- Configure servers and devices to use strong cipher suites that provide robust encryption.
- Keep encryption protocols and software up to date with the latest security patches.
#7. Maintain a Vulnerability Management Program
Use and Regularly Update Antivirus Software
Malware, viruses, and other malicious software are evolving constantly, so you need to keep your finger on the pulse of the latest security updates to identify and mitigate new and emerging threats effectively.
Tips for compliance
- Install antivirus software on all systems within the CDE, including servers, workstations, and any other devices that handle cardholder data.
- Ensure that endpoints, such as employee workstations, point-of-sale (POS) terminals, and servers, are protected by antivirus software.
- Configure antivirus software to receive regular updates to virus definitions and signatures.
- Enable automated updates whenever possible to ensure that antivirus protection is consistently up-to-date.
Develop and Maintain Secure Systems and Applications
This requirement focuses on building and sustaining a secure environment for systems and applications that handle cardholder data through consistent data security measures.
Tips for compliance
- Implement security considerations from the early stages of the Software Development Life Cycle (SDLC).
- Integrate security practices into requirements, design, coding, testing, and deployment phases.
- Perform thorough security testing, including static code analysis, Dynamic Application Security Testing (DAST), and penetration testing.
- Implement a robust patch management process to promptly apply security updates and patches.
- Regularly update software, operating systems, and third-party libraries to address known vulnerabilities.
- Conduct regular vulnerability assessments to identify and address potential weaknesses.
#8. Implement Strong Access Control Measures
Restrict Access to Cardholder Data by Business Need-to-Know
This requirement emphasizes the need to limit access to cardholder data to only those individuals who require it to perform their job responsibilities.
Tips for compliance
- Clearly define roles and responsibilities within the organization that involve access to cardholder data.
- Document the specific business processes and legitimate reasons for accessing cardholder data for each role.
- Utilize Role-Based Access Control (RBAC) mechanisms to grant access permissions based on job roles.
- Regularly review access logs to detect and investigate any unauthorized or suspicious activities.
- Update access permissions to ensure alignment with current job roles.
Assign a Unique ID to Each Person with Access to a Computer
This requirement is designed to enhance security by ensuring that every individual who has access to computer systems and cardholder data has a unique and traceable identifier.
Tips for compliance
- Assign a unique User Identifier (ID) to each person who has computer access within the organization.
- Use unique IDs with strong user authentication mechanisms, such as complex passwords, two-factor authentication, smart cards, biometrics, or multi-factor authentication.
- Promptly deactivate or update a unique ID when an employee leaves the organization or changes roles.
Debit Card Program Compliance Controls
#9. Restrict and Monitor Physical Access to Cardholder Data
This requirement is aimed at ensuring the physical security of systems and devices that store, process, or transmit cardholder data. Restricting physical access helps prevent unauthorized individuals from physically compromising cardholder data, such as through theft or tampering.
Tips for compliance
- Implement physical access control mechanisms to restrict access to areas containing cardholder data, including access control systems, key cards, biometric authentication, surveillance, visitor logs, and other security measures.
- Enforce escort policies for visitors to cardholder data areas, ensuring that they are accompanied by an authorized employee at all times.
- Incorporate procedures for responding to physical security incidents, such as unauthorized access or tampering with cardholder data.
- Regularly review and update access controls and other security controls for physical areas where cardholder data is stored.
#10. Track and Monitor Access to Network Resources and Cardholder Data
This requirement is created to enhance the security of cardholder data by implementing robust logging and monitoring mechanisms.
Tips for compliance
- Configure systems, applications, and network devices to generate logs of relevant events, including remote access activity.
- Logging should capture information about all access attempts, changes to configurations, and other security-relevant activities.
- Implement centralized logging where logs from various sources are aggregated into a central repository.
- Establish a schedule for regular reviews of log data and assign responsibility for log reviews to trained personnel or use automated tools to analyze logs.
- Logging and monitoring access to network resources and cardholder data is required, with logs being retained for at least 12 months.
#11. Regularly Test Security Systems and Processes
This requirement emphasizes the importance of conducting regular and comprehensive testing of security controls, processes, and systems to identify vulnerabilities, assess their effectiveness through self-assessment questionnaires, and ensure ongoing PCI compliance.
Tips for compliance
- Conduct regular vulnerability scans and penetration tests of systems within the CDE to test networks for weaknesses.
- Perform both internal and external vulnerability scans to identify weaknesses from both inside and outside the network perimeter.
- Conduct security assessments, which may include internal and external audits, to evaluate the effectiveness of security systems and controls against PCI DSS standards.
- Regular security testing includes conducting quarterly external vulnerability scans and performing annual penetration tests.
- Organizations must conduct quarterly vulnerability scans by Approved Scanning Vendors (ASVs) to protect sensitive information, often coordinated with a qualified security assessor.
#12. Maintain an Information Security Policy
Establish, Publish, Maintain, and Disseminate a Security Policy
This PCI requirement is necessary to ensure that organizations have a documented framework to protect cardholder data and customer data within a broader information security strategy and maintain a secure environment.
Tips for compliance
- Align the security policy with relevant PCI DSS standards and legal requirements.
- Ensure that the security policy addresses the specific obligations and recommendations outlined in PCI compliance and is validated by an internal security assessor.
- Establish a process for regularly reviewing and updating the security policy, supported by a self-assessment questionnaire.
- Update the policy to reflect changes in the organization’s infrastructure, technology, and regulatory landscape.
Conduct Regular Security Awareness Training for All Personnel
This PCI requirement is for educating all individuals within an organization about security policies, procedures, and best practices to protect cardholder data.
Tips for compliance
- Security awareness training should be provided to all personnel within the organization, including employees, contractors, and third-party vendors.
- Conduct security awareness training regularly, with a frequency that aligns with the organization’s policies and the dynamic nature of security threats. For example, recognizing and avoiding phishing attacks.
- Provide security awareness training as part of the onboarding process for new employees.
- Establish feedback mechanisms for employees to provide input on the effectiveness of training programs.
Conclusion
On average, it takes around 21 days to achieve PCI compliance if you know how to do it right.
We at SPD Technology have years of experience building products in the Fintech industry, ensuring systems remain PCI DSS compliant with all required standards and regulations. Feel free to contact us for help, and build a payment solution that will help you take the lead in your market.

